SMS fraud: The complete guide to detection and prevention
Understand the major types of SMS fraud in 2026 and the concrete steps businesses and mobile operators can take to detect and prevent them.

SMS fraud costs businesses and consumers billions every year and it is getting harder to catch. Global losses from SMS fraud are projected to reach $71 billion in 2026, even as the industry invests more than ever in defenses. At the same time, the nature of SMS fraud is shifting: AI-powered smishing campaigns now achieve click-through rates of up to 54%, and SMS pumping fraud, where fraudsters drain business SMS budgets by flooding verification endpoints with fake numbers, has become the most severe threat to the A2P SMS ecosystem.
This guide covers every major type of SMS fraud, how to detect it before it causes damage, and the specific steps businesses and mobile operators can take to prevent it.
What is SMS fraud?
SMS fraud is when bad actors misuse SMS to deceive individuals or organizations for financial gain or other purposes. Fraudsters exploit weaknesses in SMS infrastructure, human psychology, and business systems, stealing personal data, draining SMS budgets, or manipulating the revenue structures of mobile networks.
SMS fraud is widespread because SMS remains one of the most universally accessible communication channels. It works on every phone type, gets delivered and opened almost instantly, and carries an inherent sense of legitimacy, which is exactly what fraudsters exploit.
What has changed in 2026 is the sophistication of the attacks. Fraud losses are declining in raw dollar terms, but this does not mean the problem is being solved. It reflects AI-powered security tools catching more attacks, while fraudsters simultaneously evolve their methods: using AI to personalize attacks, automating SMS pumping at industrial scale, and organizing smishing campaigns across hundreds of thousands of fraudulent domains.
Types of SMS fraud
There are many ways criminals exploit SMS. The Mobile Ecosystem Forum has identified 14 distinct types of SMS fraud, organized into four categories: identity theft, data theft, network manipulation, and commercial exploitation. Below are the most significant.
1. Smishing (SMS phishing)
Smishing is a type of fraud where criminals send SMS messages designed to trick recipients into revealing personal or financial information, including sensitive information such as credit card numbers, social security numbers, and account numbers, clicking malicious links, or downloading malware. It is the SMS equivalent of email phishing and increasingly, it is the dominant form of mobile phishing.
70% of all mobile phishing attacks now take place over SMS, and SMS-originated scams surged 40% year-on-year in 2025. A smishing message typically impersonates a trusted brand; a bank, package delivery service, tax authority, or government agency, creating urgency to prompt the victim to act without thinking.
Sophisticated attacks use social engineering: fraudsters research targets on social media and breached databases to craft messages that feel personal and legitimate. The recipient sees their bank’s name in the sender ID, a reference to a recent transaction, and a link to what looks exactly like their bank’s login page.
AI-powered smishing: The 2026 threat
The most significant evolution in smishing is the use of AI to generate and personalize attacks at scale across messaging platforms. Key developments in 2026:
- AI personalization: Fraudsters use breached databases and social media data to generate messages that reference real names, account details, and recent activity, making them indistinguishable from genuine communications.
- Deepfake SMS: AI-generated messages that mimic the writing styles of known contacts, enabling “Hi Mum/Dad” and “Wrong Number” scams.
- Industrial-scale criminal networks: Groups such as the Smishing Triad operate using 100,000+ fraudulent domains, rotating infrastructure faster than blocklists can keep up.
- Multi-channel escalation: 41% of phishing incidents now involve SMS combined with voice calls or email to increase credibility.
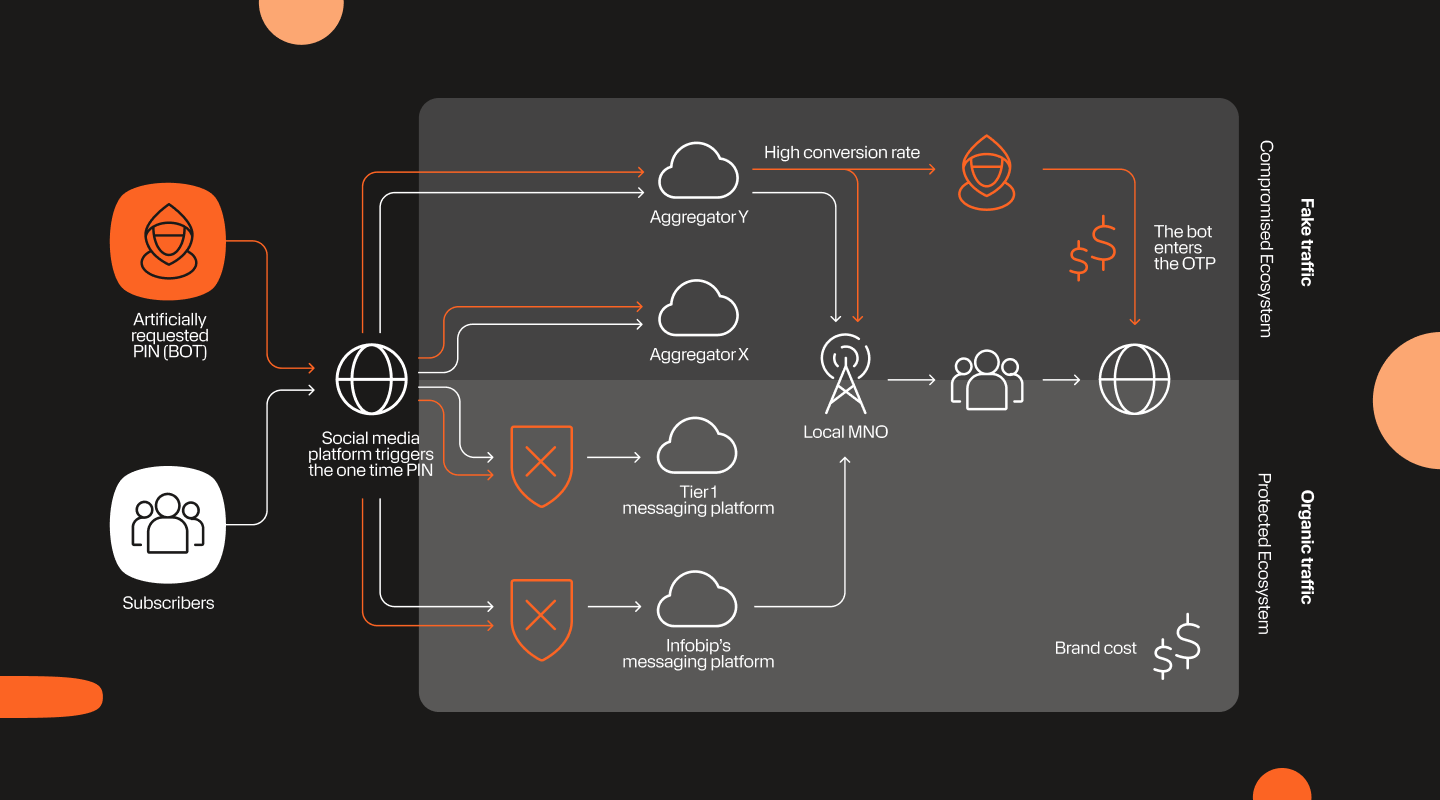
2. SMS pumping fraud (Artificially inflated traffic / AIT)
SMS pumping fraud, also known as Artificially Inflated Traffic (AIT), SMS toll fraud, or International Revenue Share Fraud (IRSF), is a type of fraud where criminals artificially generate large volumes of SMS messages to extract revenue from a business’s SMS budget. Unlike smishing, SMS pumping targets businesses directly, not consumers.
How SMS pumping fraud works – Step by step
- The fraudster establishes a revenue share arrangement with a premium-rate carrier or mobile network operator (MNO). This is the financial engine of the fraud: the MNO agrees to pay the fraudster a share of revenue for every SMS message delivered to numbers on their network.
- The fraudster identifies a target business endpoint, typically an SMS-based OTP (one-time password), phone verification, or account registration flow on a website or app.
- Bot scripts flood the endpoint with fake phone numbers. These are real numbers registered to the premium-rate MNO, so messages are actually delivered, triggering the revenue share. The bot may use sequential number ranges, or rotate through numbers to avoid rate-limit detection.
- The business pays per message sent, not per message verified. Every OTP message sent is billed at the standard A2P SMS rate, regardless of whether a real user ever entered the code.
- The fraudster collects the MNO revenue share. The business absorbs the full cost; the fraudster and MNO split the A2P revenue. Fraudsters can generate thousands of fake OTP requests per minute.
3. SMS spoofing
SMS spoofing changes the sender information on a text message so that the recipient sees a name or number chosen by the sender, rather than their actual number. Showing name instead of number is not illegal. Legitimate uses include bulk service messages and emergency alerts from government agencies.
The problem arises when fraudsters use spoofing to impersonate trusted brands as part of smishing campaigns. By spoofing the sender ID of a bank, delivery company, or employer, they make their fake messages appear in the same SMS thread as genuine messages from that sender, giving the attack an added layer of credibility. Recipients should treat any message from an unknown sender with caution. A common variant is faking payment confirmation texts to facilitate high-value purchase fraud on buy-and-sell platforms.
4. SIM swapping
SIM swapping is when fraudsters abuse the legitimate SIM card porting process to take over a victim’s mobile number. By contacting the victim’s mobile operator and using social engineering, or leaked personal data, to impersonate the account holder, the fraudster convinces the operator to transfer the number to a SIM card they control.
Once the number is ported, the fraudster intercepts all calls and SMS messages sent to that number, including the two-factor authentication (2FA) codes needed to gain access to their bank account, email, and other accounts. The victim’s phone simply stops receiving signal.
In 2026, mobile operators usually require port-out authorization; a PIN or in-store verification before processing a SIM swap, making attacks harder. SIM swap detection is available for enterprises via the SIM Swap network API provided by Infobip. Once implemented, enterprises can receive real-time information when a customer’s SIM has recently been swapped, enabling them to block authentication attempts until the account holder is reverified.
5. SMS trashing
SMS trashing is a fraud carried out by rogue SMS aggregators. Messages are accepted from a sending business and charged at full price, but instead of being delivered to the recipient’s mobile number, they are discarded on the aggregator’s platform. The aggregator collects the full A2P rate from the business without paying out the delivery fee to the mobile operator, since no delivery ever occurred.
The business sees messages marked as sent, but delivery rates and engagement metrics quietly decline. SMS trashing was identified as a significant emerging fraud type by the Mobile Ecosystem Forum in 2021 and remains a concern for businesses using lower-quality or unverified aggregator routes.
6. Grey routes and SIM boxes
Grey routes are paths through which A2P SMS messages, which should be charged at commercial rates, are misrouted through cheaper person-to-person (P2P) infrastructure. This allows rogue mobile operators or aggregators to undercut legitimate routes and avoid paying the agreed market rates to the operators who actually deliver the messages.
There are three main grey route types:
- Operator-to-operator: A rogue operator masks A2P commercial traffic as P2P under a roaming agreement, avoiding A2P charges.
- A2P aggregator routing: An operator uses a local aggregator to route traffic via cheaper SMPP (Short Message Peer-to-Peer) connections, avoiding premium international A2P rates.
- SIM boxes: Physical devices loaded with prepaid P2P SIM cards used to route A2P traffic at P2P prices. The difference in cost, which can be substantial, is pure margin for the fraudster.
Grey routes remain a problem in 2026, even in markets with A2P 10DLC registration (the US sender registration framework). Registration reduces grey route opportunities for registered senders, but unregistered traffic and international routes remain vulnerable. The practical impact for businesses is lower delivery quality, reduced compliance (messages may not carry legal disclaimers), and unreliable sender IDs.
7. SMS spam
SMS spam is unsolicited commercial messaging sent at scale to mobile numbers, typically without consent. A 2026 report found Americans receive over 19 billion spam texts per month.
Beyond being an annoyance, SMS spam erodes the general trustworthiness of SMS as a channel and violates compliance laws in almost every jurisdiction. As anti-spam measures on voice calls have improved, spammers have increasingly shifted to SMS. The practical defense sits primarily with mobile operators and their SMS firewalls, rather than with individual recipients.
The impact of SMS fraud
SMS fraud inflicts losses across the entire mobile ecosystem; consumers, businesses, and mobile operators all bear costs.
For consumers, the impact ranges from financial loss through smishing and account takeover, to identity theft following SIM swapping attacks. The US Federal Trade Commission reported $470 million in text scam losses for 2024 – five times higher than what was reported in 2020.
For businesses, SMS pumping is the most direct financial threat. The cost arrives invisibly, through inflated SMS invoices, and is often only noticed after significant spend has already occurred. For companies using SMS OTP at scale, a single undetected pumping campaign can generate tens of thousands of dollars in fraudulent charges within hours.
For mobile operators and the telecom industry, the CFCA Global Fraud Loss Survey estimated $41.82 billion in global telecom revenue lost in 2025, up from $38.95 billion in 2023. Grey routes, SIM boxes, and revenue-share fraud structures all undermine the legitimate economics of the A2P SMS ecosystem, leading to higher prices for legitimate senders and degraded delivery quality across the board.
Beyond direct financial losses, SMS fraud erodes trust in the channel itself. As consumers learn to distrust SMS messages, the effectiveness of legitimate business communications, such as delivery notifications, OTP codes, appointment reminders, declines.
How to detect and prevent SMS fraud
Early detection is the difference between a minor anomaly and a major financial loss. Different fraud types leave different signals, knowing what to look for, and where, is the first line of defense.
Detecting SMS fraud: Key signals by type
SMS fraud does not announce itself. The signals vary by fraud type, and many go unnoticed until the damage is already done. Below are the primary indicators for each major category.
- SMS pumping: A sudden spike in SMS send volume without a matching increase in user registrations or conversions is the clearest signal. Watch for low OTP conversion rates (below 20%), traffic concentrated in unusual country codes, off-hours request bursts, sequential number ranges in OTP requests, and multiple requests from the same IP or device fingerprint. By the time these show up on an invoice, a campaign may have already cost thousands. Infobip Signals is built specifically to detect these patterns in real time, flagging anomalous traffic before it becomes a billing problem.
- Smishing: For businesses, the signal is usually inbound – customer support tickets reporting suspicious messages appearing to come from your sender ID, or flagging suspicious activity on their accounts, or employees flagging SMS messages impersonating internal teams (IT, HR, finance). Credential reuse alerts and unusual login spikes following high SMS delivery volume can also indicate that a smishing campaign targeting your brand is in progress.
- SMS spoofing: Spoofing is most visible through customer complaints. If recipients report receiving messages that appear in the same SMS thread as your legitimate messages but with unexpected content, your sender ID is being spoofed. Monitoring brand mentions and maintaining a customer reporting channel helps surface this early.
- SIM swapping: It is a significant threat for businesses that have been slow to implement SIM swap detection solutions. The real user loses signal and can no longer receive OTP codes, while the attacker intercepts them. SIM swap detection services monitor IMSI register changes and can alert in real time when a customer SIM has recently been ported.
- Grey routes and SMS trashing: These manifest as degraded delivery metrics – higher undelivered rates, inconsistent delivery times, or messages marked as sent that never reach recipients. If delivery rates drop unexpectedly without a network explanation, rogue routing is a likely cause.
- SMS spam: For mobile operators, the signal is traffic pattern anomalies at the network level – unusually high volumes from single senders, high complaint rates, or traffic that bypasses normal A2P registration. For businesses, receiving spam complaints from your own subscribers may indicate your sender ID or routes are being misused.
How to prevent SMS fraud
Effective prevention requires layered defenses – no single measure stops all fraud types. The measures below cover the full spectrum of SMS fraud, from infrastructure-level attacks to social engineering.
1. Secure your SMS-sending infrastructure
The foundations of SMS fraud prevention sit at the infrastructure level – rate limiting, bot detection, and API hardening apply across fraud types, but are especially critical for stopping SMS pumping and unauthorized mass sends.
- Rate limiting: Set appropriate per-number, per-IP, and per-device fingerprint limits on SMS-triggering endpoints. Legitimate users rarely request more than one or two OTPs within a short time window, so repeated requests beyond that threshold can be safely restricted. Apply exponential backoff once limits are exceeded.
- Bot detection: Deploy behavioral analysis and device fingerprinting on every endpoint that triggers an SMS send – registration forms, OTP flows, password reset pages. Traditional CAPTCHA is increasingly less effective. Modern bots equipped with AI can solve visual challenges faster than humans, and services like 2Captcha automate CAPTCHA bypassing at low cost. More effective CAPTCHA alternatives include invisible behavioral analysis, device fingerprinting, and AI-driven bot scoring, all of which stop bots without adding friction for real users.
- API security: Treat SMS-sending APIs as financial endpoints. Enforce IP whitelisting for server-to-server calls, require OAuth for client-side integrations, rotate API keys on a defined schedule, and log all calls – anomalous patterns are often the first signal of fraud in progress.
2. Verify phone numbers before sending
A number lookup API run before any SMS send lets you screen out the number types most commonly exploited in SMS fraud:
- Premium-rate numbers registered to revenue-share carriers – the financial engine of SMS pumping.
- Disposable and virtual numbers generated specifically to trigger OTP sends at scale.
- Numbers inconsistent with the user’s stated location or registration context.
Geo-restrictions allow this: restrict SMS sending to countries where your business has real users. An allowlist of permitted country codes is more robust than a blocklist and eliminates the majority of risk from high-fraud number ranges with a single control.
3. Protect against smishing and social engineering
Smishing targets people, not systems. Prevention here is a combination of authentication hygiene, user education, and brand monitoring.
- Reduce SMS OTP exposure: SMS OTP is acceptable for most risk levels, but phishing-resistant alternatives (FIDO2, hardware security keys, authenticator apps) should be used for privileged access and high-value transactions where SIM swapping or smishing could lead to account takeover.
- Train employees: Smishing campaigns frequently impersonate internal teams – IT helpdesk, HR, finance. Employees should know the signs and have a clear, low-friction way to report suspicious messages.
- Verify before acting: Communicate to customers and staff to always verify unexpected requests through a second channel – call the number on the official website, not the one in the message.
- Monitor your sender ID: Set up a reporting channel for customers to flag suspicious messages appearing to come from your brand. Spoofed sender IDs are detected fastest through customer reports, not internal systems.
- Mobile device management (MDM): For corporate devices, MDM provides an additional layer through managed DNS filtering and app controls that can block known smishing infrastructure.
4. Guard against SIM swapping
SIM swapping attacks the authentication layer itself – once a number is ported, the attacker intercepts every SMS sent to it, including OTP codes.
- Use SIM swap detection services: Use them to alert your systems when appropriate and detect if a customer’s SIM has recently been swapped. Block or step up authentication for any account where a SIM swap has been detected within a defined window.
- Require step-up verification for high-risk actions: If a SIM swap is detected, require additional authentication (app-based, email, or identity verification) before allowing access to sensitive account functions.
- Inform users: Educate customers on how to take proper security measures. Also, share information about ongoing fraudster attacks or where they can find this information.
5. Use verified SMS routes and monitor delivery quality
Grey routes primarily impact message quality, deliverability, and regulatory compliance. They can introduce variability in delivery performance, bypass carrier registration requirements, and make cost structures less predictable.
- Use registered, verified aggregators or direct routes: Work only with SMS providers that operate on legitimate A2P routes with transparent routing practices, or where possible, use direct operator connections. This reduces exposure to routing inefficiencies and improves deliverability consistency.
- Monitor delivery rates continuously: A drop in delivery rates or a rise in undelivered messages without a clear network explanation can indicate routing issues. Establish baseline delivery metrics and alert on deviations.
- A2P sender registration: In markets with sender registration frameworks (such as A2P 10DLC in the US), register all senders. This improves deliverability for legitimate traffic and helps meet carrier compliance requirements.
6. Real-time monitoring and automated alerts
Manual monitoring is insufficient at scale. Automated alerts across the following metrics give you the response window to intervene before fraud becomes a significant cost or trust event:
- SMS send volume exceeding a defined threshold within a rolling time window.
- OTP conversion rate dropping below a defined threshold (e.g., 20%).
- SMS spend reaching a defined percentage of monthly budget mid-period.
- Unusual concentration of outbound traffic to specific country codes.
- Delivery rate dropping below baseline without a network explanation.
- Spike in customer reports of unexpected or suspicious messages from your sender ID.
How Infobip detects and protects against SMS fraud
Infobip operates two complementary layers of SMS fraud protection: an SMS firewall for mobile operators, and Infobip Signals for enterprises and businesses using SMS at scale.
The Infobip SMS firewall operates at the network level, protecting mobile operators and their subscribers. It connects to a continuously updated database of malicious numbers and URLs, uses machine learning for proactive threat detection, and provides automated responses to identified threats, including MSISDN reputation analysis and SIM box detection. The firewall has demonstrated less than 0.1% false-positive rates in production deployments. The Infobip SMS firewall was the first in the industry to detect a previously unknown fraud type spreading globally, identifying an unusual traffic pattern that bypassed international message charges through a third-party app. Mobile operators were briefed and the firewall updated to block the pattern automatically.
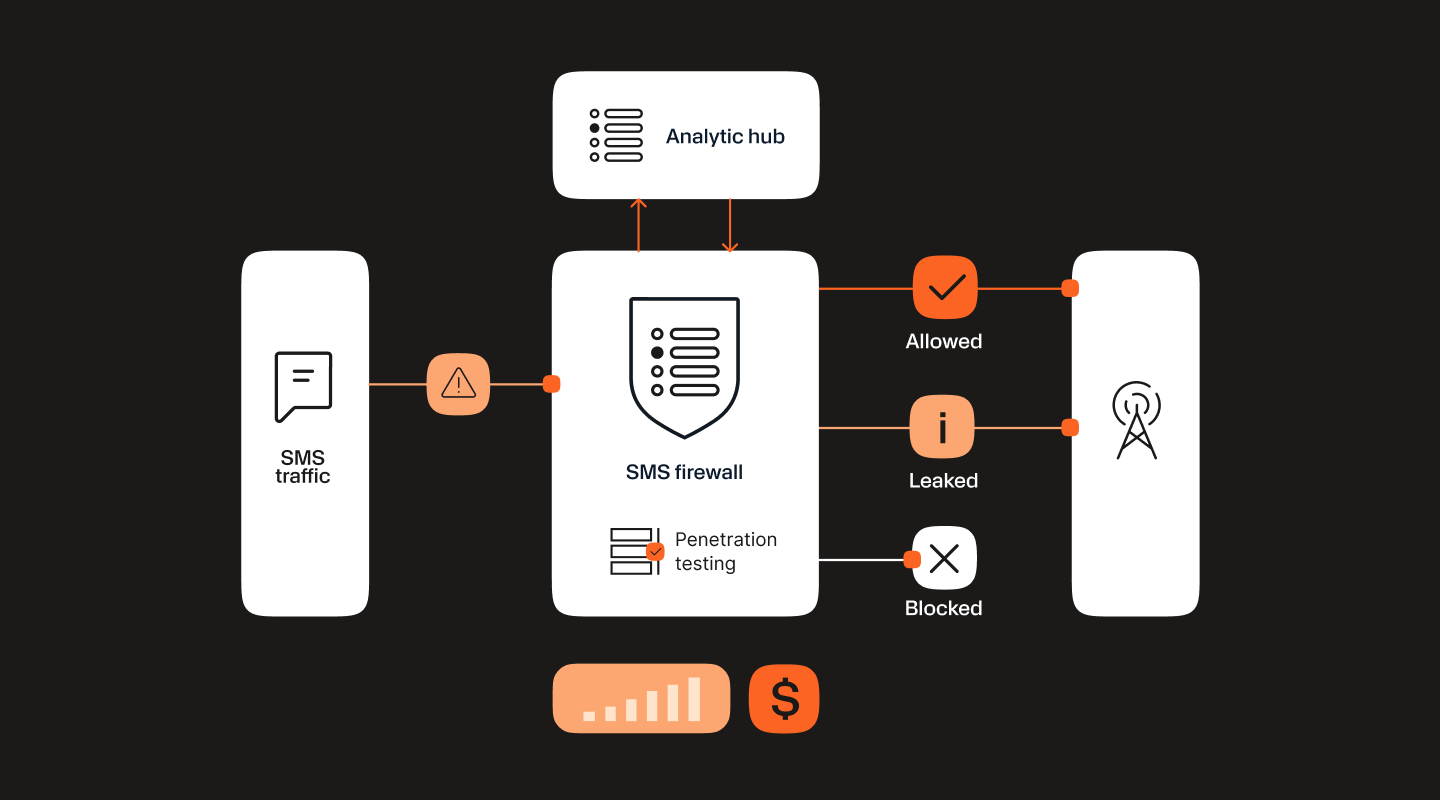
Besides an SMS firewall, we also use a simple plug-and-play solution called Infobip Signals that uses a mix of methods to spot and stop fraud, particularly for OTP traffic. It checks for unusual patterns and behaviors, uses data analysis to assess risks, and employs machine learning to block fake traffic as it happens.
You can check out an overview of Signals in this video:
Next, the UK fashion retailer, deployed Infobip Signals to protect their high-volume SMS OTP flows, with approximately 175,000 artificial messages blocked per month, and no disruption to legitimate customer communications.
The future of SMS fraud prevention
The overall trajectory of SMS fraud in 2026 is lower losses, higher sophistication, and the prevention landscape is adapting in kind. Fraud losses are declining in aggregate, not because attacks have stopped, but because detection tools, industry standards, and regulatory pressure are starting to catch up with fraudsters.
AI-powered detection is becoming the baseline. Just as fraudsters use AI to personalize smishing at scale, security vendors and mobile operators are deploying AI for real-time anomaly detection, behavioral analysis, and traffic pattern recognition. The arms race is escalating on both sides, but detection tooling, including operator-level SMS firewalls and enterprise traffic monitoring, is now sophisticated enough to catch fraud types that would have been invisible a couple of years ago.
Alternative and complementary authentication methods are becoming the new standard. For most consumer-facing use cases at moderate risk levels, SMS OTP remains widely deployed and acceptable, but businesses should audit where it sits in their authentication stack and replace it where the risk profile demands it. NIST and other standards bodies have been moving away from recommending SMS OTP for high-security applications for several years, citing SIM swapping and smishing vulnerabilities. In 2026, this shift is accelerating. Phishing-resistant alternatives, such as FIDO2 passkeys, hardware security keys, authenticator apps, are becoming the standard for privileged access and high-value transactions.
Collective industry defense is strengthening. The GSMA Fraud and Security Group (FASG), i3Forum, and national telecom regulators are increasingly coordinating on fraud intelligence sharing, common SMS firewall standards, and operator-level content inspection. Poland’s Act on Combating Abuses in Electronic Communication, requiring operators to block smishing and sender ID spoofing, is an example of the legislative direction other markets are following.
Prevention is moving from reactive to proactive. The businesses and operators best positioned for this environment are those that treat SMS fraud prevention as an ongoing discipline: layering technical controls, real-time monitoring, staff awareness, and industry collaboration, rather than a one-time compliance checkbox reviewed annually.